Title
Create new category
Edit page index title
Edit category
Edit link
Device Integrity Signals
TrustX Device Integrity Signals collect rich, high-fidelity telemetry from every web and native session. Device signals can be used to uniquely identify visitors and additional device signals (for example, if a device is rooted/ jailbroken) that can be applied for further fraud analysis.
Signal Types
Data captured by Device Integrity Signals can include the following information.
Network and Environment
- Bot Detection — Identifies automated browsers and headless agents
- TOR Exit Node — Detects sessions originating from TOR network
- VPN Detection — Flags known VPN and anonymising proxies
- Proxy Detection — Identifies traffic routed through open/anonymous proxies
- MITM Detection — Detects Man-in-the-Middle interception attempts
- Location Spoofing — Identifies GPS or location manipulation
Mobile Device Signals
- Rooted Device — Android root detection
- Jailbroken Device — iOS jailbreak detection
- Emulator — Detects Android emulators and iOS simulators
- Cloned App — Identifies app cloning/dual-space tools
- Factory Reset — Detects recent device resets
- Frida/Instrumentation — Detects dynamic instrumentation runtime frameworks
- Virtual Machine (VMs) — Flags execution within VMs
Browser Signals
- Incognito Mode — Detects private/incognito browsing sessions
- Developer Tools — Flags if DevTools are open during a session
- Visitor ID — Stable browser fingerprint (persists unless browser reset)
Enabling Device Integrity Signals
Before utilizing Device Integrity Signals, it is required to enable the service in the Backoffice. This is a prerequisite that must be enabled before the service will work.
Device Integrity Signals can be enabled from the Backoffice by following the instructions below:
- Log in to the Backoffice application.
- Expand the System Management tab and find - System Management > Settings.
- Under General settings, click the "Enable Device Integrity Signals" toggle.

Possible Regions and values include:
| Region | Value |
|---|---|
| Europe | EU |
| United States | US |
| Asia-Pacific | AP |
- Click the 'Save Changes' button to finalize the changes.
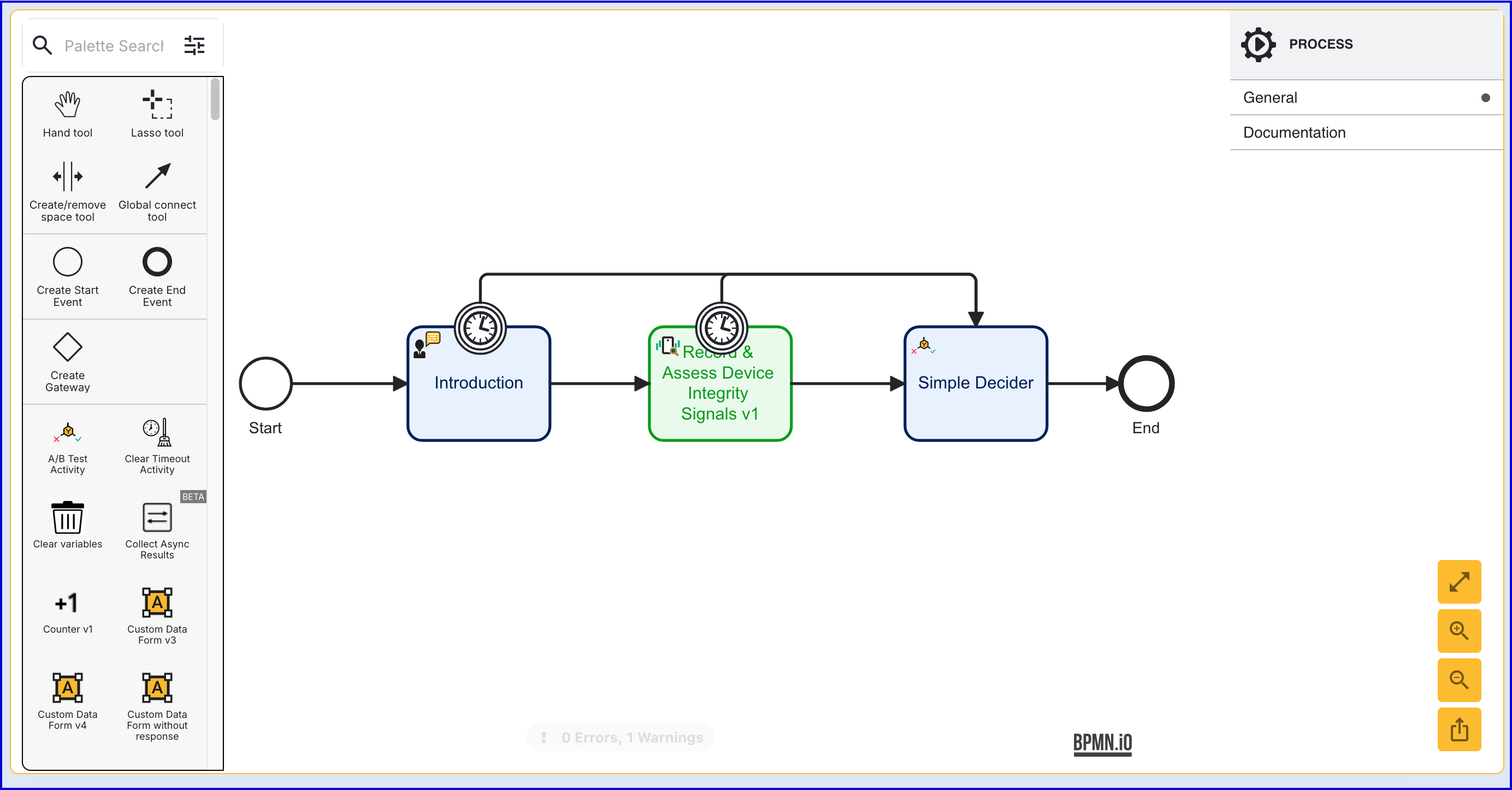
Configuring a Process Definition
This section will describe integrating Device Integrity Signal functionality into a Process Definition using the 'Record & Assess Device Integrity Signals v1' activity. For more information on creating a Process Definition and using the Process Designer, see the Process Definition Guide.
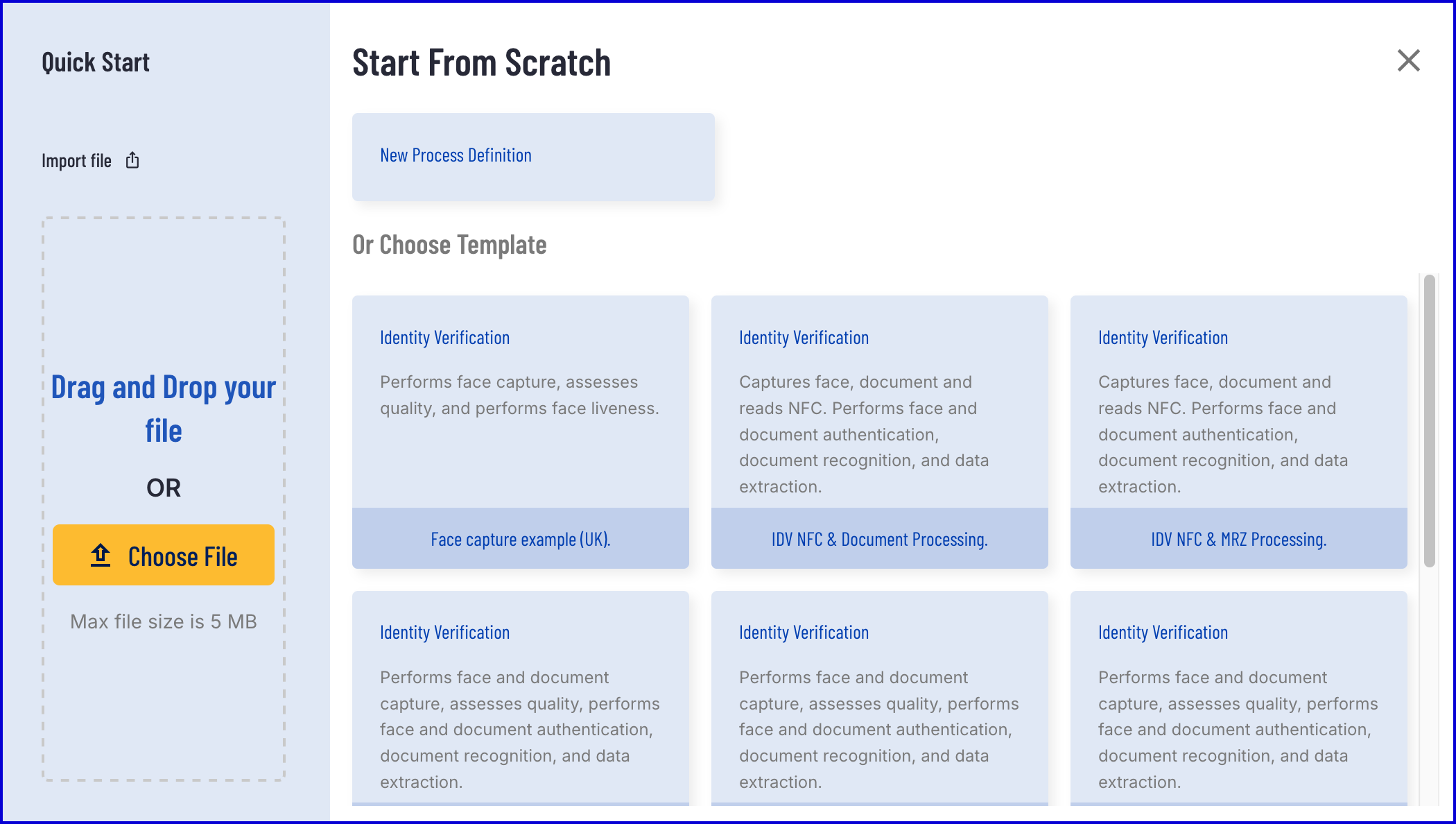
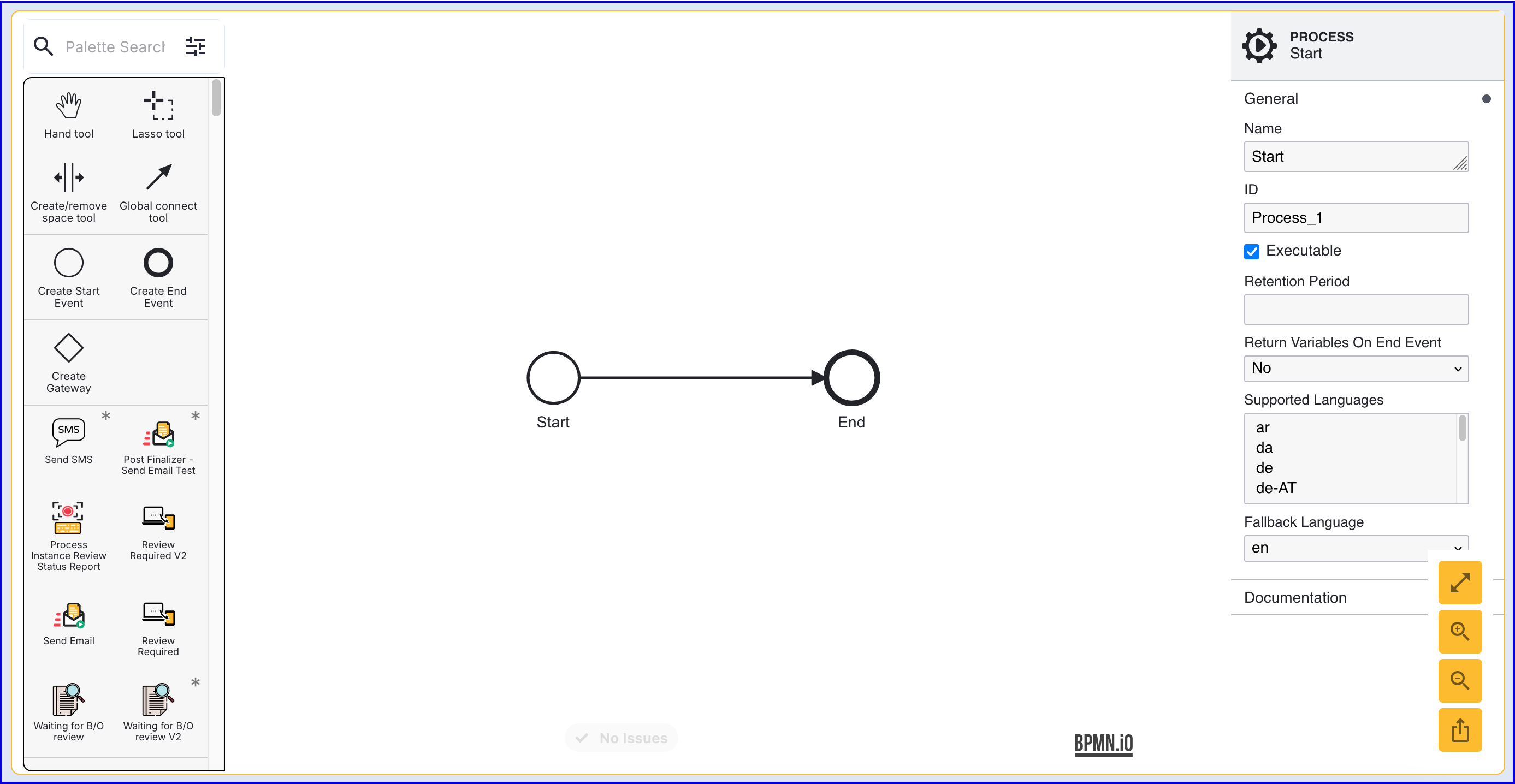
Step One - Create a new Process Definition
To start, create a new Process Definition by following the steps outlined below.
- Navigate to the Process Definitions page found in the left-side navigation bar of the Backoffice.
- Click the 'New Process Definitions' button to open the Process Definition pop-up modal. For this example, a Process Definition will be created from scratch.
- To start a basic Process Definition in the Process Designer, add a 'Start Event' and 'End Event' and connect them using the Global connect tool.
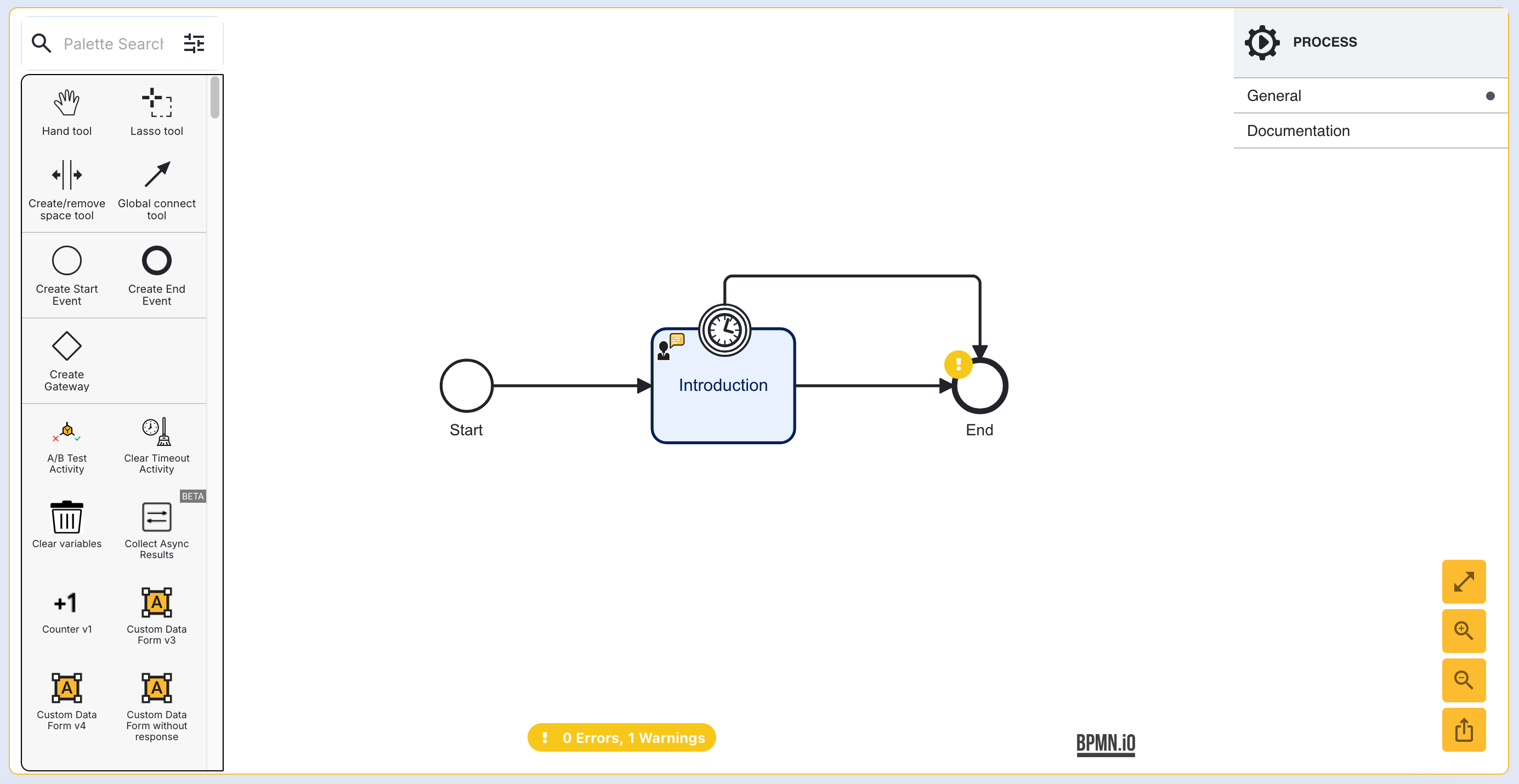
- Optionally add an 'Introduction' at the beginning of the Process Definition to welcome the user.
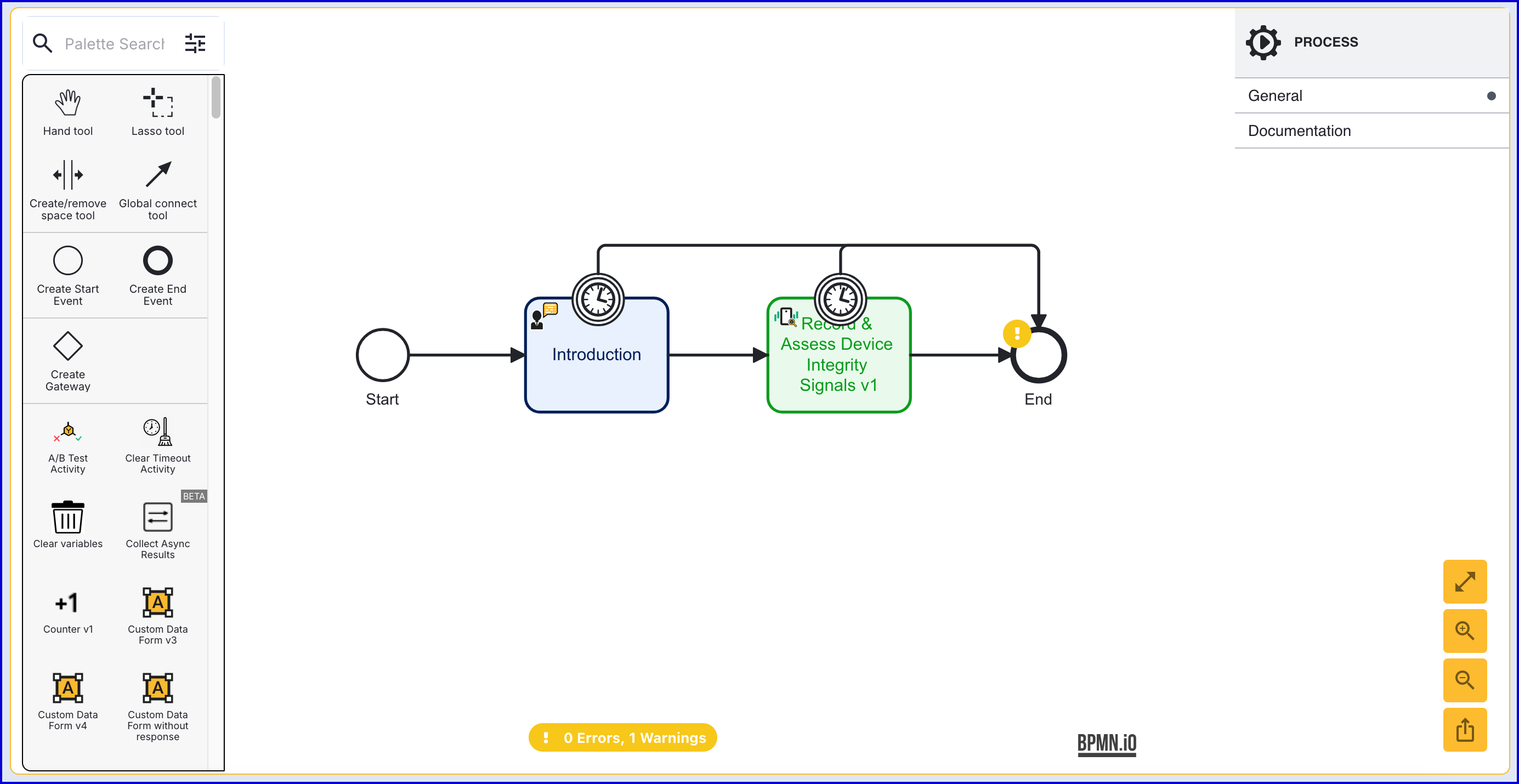
Step Two - Configure the Device Integrity Signals Activity
This step will involve integrating the 'Record & Assess Device Integrity Signals' activity and configuring the various input parameters.
- Before the 'end' even, add a 'Record & Assess Device Integrity Signals' activity to the flow and connect it using the Global connect tool. Multiple 'Device Integrity Signal' activities can be included in a single Process Definition, differentiated using the Signal Key.
- The activity includes the following configurable input parameters. All listed checks can be enabled or disabled based on the specified input parameters. Some of the listed checks are platform specific that only affect web or native configurations.
| Parameter | Description | Type | Default |
|---|---|---|---|
| Browser bot Detection Check Enabled | Check that determines whether the browser is using an automated bot. | Boolean | ${true} |
| Browser Developer Tools Detection Check Enabled | Check that determines whether the browser is using developer tools. | Boolean | ${true} |
| Browser Incognito Detection Enabled | Check that determines whether the browser is using an incognito mode. | Boolean | ${true} |
| Browser Privacy Focussed Detection Check Enabled | Check that determines whether the web browser is a privacy focussed browser. | Boolean | ${true} |
| Browser Tamper Detection Check Enabled | Check that determines whether intentional changes to the browser settings, configuration or extension have been made. | Boolean | ${true} |
| Browser Virtual Machine Detection Check Enabled | Check that determines whether the browser is running on a virtual machine. | Boolean | ${true} |
| Browser VPN Detection Check Enabled | Check that determines whether the browser is runing on a VPN. | Boolean | ${true} |
| Circuit Breaker Failure Rate Threshold Percentage | Percentage of calls that must fail before the circuit is broken. Minimum value is 1. Maximum value is 100. | Integer | ${10} |
| Circuit Breaker Window Size | Time in seconds over which the circuit breaker is calculated. Default value is 5 minutes. Minimum value is 5 minutes. Maximum value is 600 minutes. | Integer | ${300} |
| Cloned App Detection Check Enabled | Determines whether the device is running a cloned application to complete the process. | Boolean | ${true} |
| Device Integrity Signal Key | The identifier of the Device Integrity Signal. | Boolean | ${true} |
| Emulator Detection Check Enabled | Check whether the Process Instance is performed on an emulator. | Boolean | ${true} |
| Enable Fail Open Circuit Breaker | A configuration that enables a circuit breaker if there is a flood of failures to decrypt the Device Integrity Signal payload. | Boolean | ${true} |
| Factory reset Detection Check Enabled | Check whether the device has been factory reset. | Boolean | ${true} |
| Factory reset Detection Check Enabled | Check whether the device has been factory reset. | Boolean | ${true} |
| Frida Detection Check Enabled | Check that determines the use of the Frida dynamic instrumentation toolkit. | Boolean | ${true} |
| Jail Broken Detection Check Enabled | Check that determines whether the device has been jail broken. | Boolean | ${true} |
| MitM Attack Detection Check Enabled | Check to determine whether a Man in the Middle (MitM) attack has been detected. This check is only avaivalable for Android devices. | Boolean | ${true} |
| Network Proxy Detection Check Enabled | Determines whether the user's internet traffic is being routed through a network proxy. | Boolean | ${true} |
| Network Tor Detection Check Enabled | Determines whether the user's internet traffic is being routed through the Tor network. | Boolean | ${true} |
| Replay Time (seconds) | The time in seconds that Client Data is allowed to be generated and processed. Minimum value is 30s. Maximum value is 990s. | Integer | ${60} |
| Root Apps Detection Check Enabled | Determines whether the application has been rooted (given superuser privileges). | Boolean | ${true} |
| Starting Component ID | The name of the step to be sent to the UI. | String | signals |
| Tampering Detection Check Enabled | Determines whether the application has been tampered with. | Boolean | ${true} |
| Test Mode | When enabled, replay checks are not performed and the user is able to submit a JSON objct instead of the sealed response from the Device Integrity Signals service. | Boolean | ${true} |
| UI Component ID | The name of the screen used in the capture UI. | String | signals |
- The 'Record & Assess Device Integrity Signals' contains several checks relating to the recorded device details. For this purpose, adding a 'Simple Decider' that determines the final decision of the Process Instance is recommended.
Circuit Breaker
A circuit breaker is included as part of the Device Integrity Signals functionality. This is used when repeated missing device integrity payloads is not mistaken for fraud from the customer.
This is important in the following scenarios:
- The front end (web / TrustSDK) cannot generate a result, or
- The sealed payload cannot be decrypted on the backend.
In those cases, the continue request from the front-end reaches Process Server, but either:
- There is no device signals payload at all (empty payload), or
- Decryption fails frequently.
Without a circuit breaker the service would always mark the Device Signals check as FAIL, which is wrong when the root cause is a vendor outage and not user/device behavior.
The circuit breaker detects a potential outage and and will treat no‑payload as N.A and log ‘circuit broken’ instead.
The circuit breaker can be enabled via the 'Record & Assess Device Integrity Signals' activity. In the activity input parameters, find the 'Enable Fail Open Circuit Breaker' input parameter. Set this parameter to true to ensure the circuit breaker is active.
Integrity Check Platform Availability
The table below describes supported platforms for each check available as part of Device Integrity Signal integrity feature.
Where listed, SDK versions represent the versions from which the listed check can be detected.
| Check | Desktop Browser Support | iOS Support | Android Support |
|---|---|---|---|
| Browser Bot Detection | Yes | Yes | Yes |
| Browser Developer Tools Detection | Yes | Yes | Yes |
| Browser Incognito Detection | Safari, Chrome | Safari, Chrome | Chrome, Samsung Browser, Firefox |
| Browser Privacy Focused Detection | Yes | Yes | Yes |
| Browser Tamper Detection | Yes | Yes | Yes |
| Browser Virtual Machine Detection | Yes | Yes | Yes |
| Browser VPN Detection | Yes | Yes | Yes |
| Cloned App Detection | No | No | Yes |
| Emulator Detection | No | No | Yes |
| Factory Reset Detection | No | Yes | Yes |
| Frida Detection | No | iOS SDK | Android SDK |
| Jail Broken Detection | No | iOS SDK | No |
| MitM Attack Detection | No | No | Android SDK |
| Network Proxy Detection | Yes | Yes | Yes |
| Network Tor Detection | Yes | Yes | Yes |
| Root Apps Detection | No | No | Android SDK |
Captured Device Integrity Data
Recorded Device Integrity Signals data is stored in the _signals variable.
Example:
xxxxxxxxxx{ "_signals": {...}}Viewing Check Results
Check results can be viewed from the Backoffice application by navigating to the Process Instance page.
- In the Backoffice application, navigate to the Process Instances page and find the name of the individual Process Instance where Device Integrity Signals was performed.
- Under the 'Checks' section, find the deviceSignals entry.
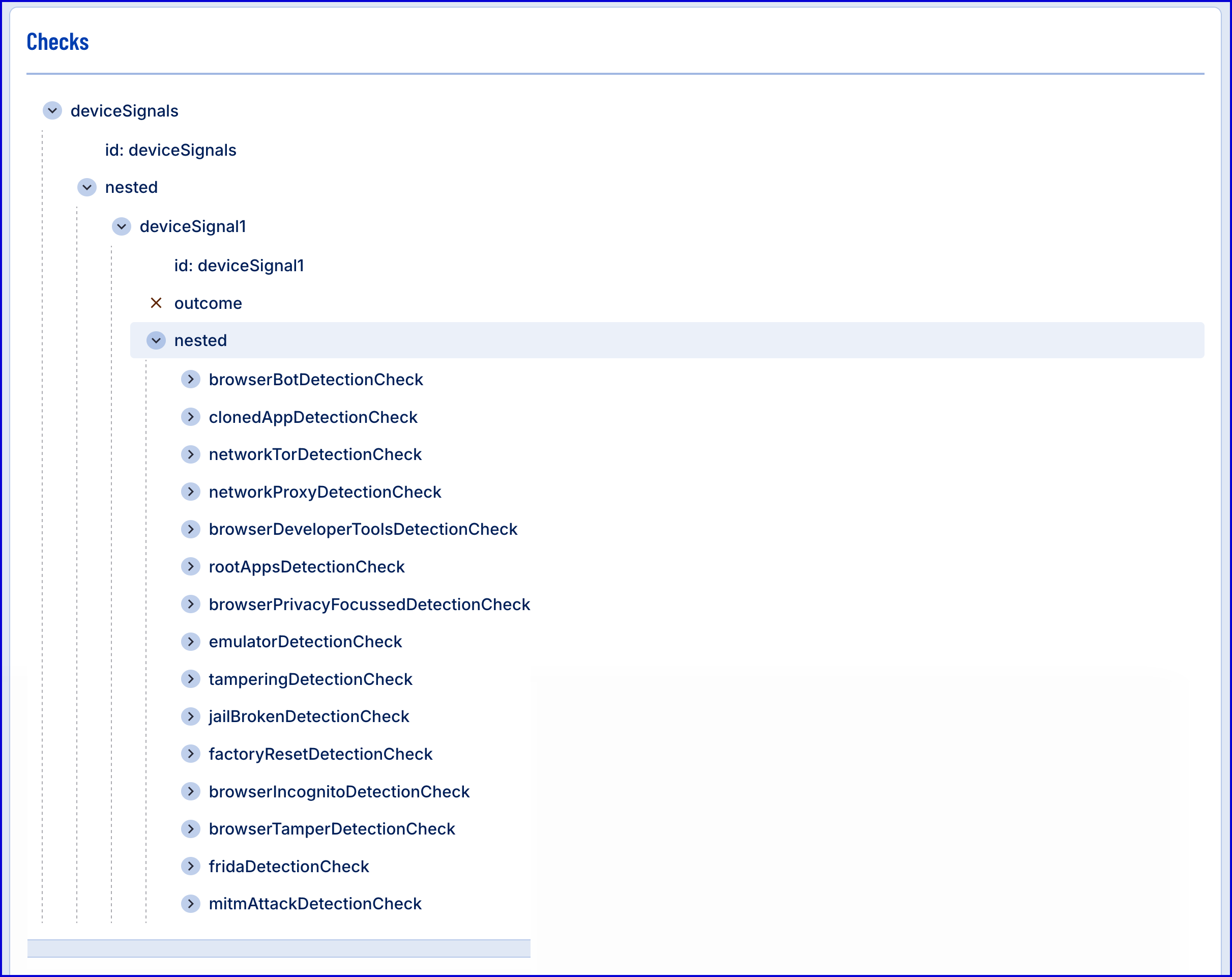
- A full list of checks performed and the results can be found in this section.
View Device Integrity Signal Details
Under the Device Integrity Signals, full details about the captured device and the integrity checks performed can be found.
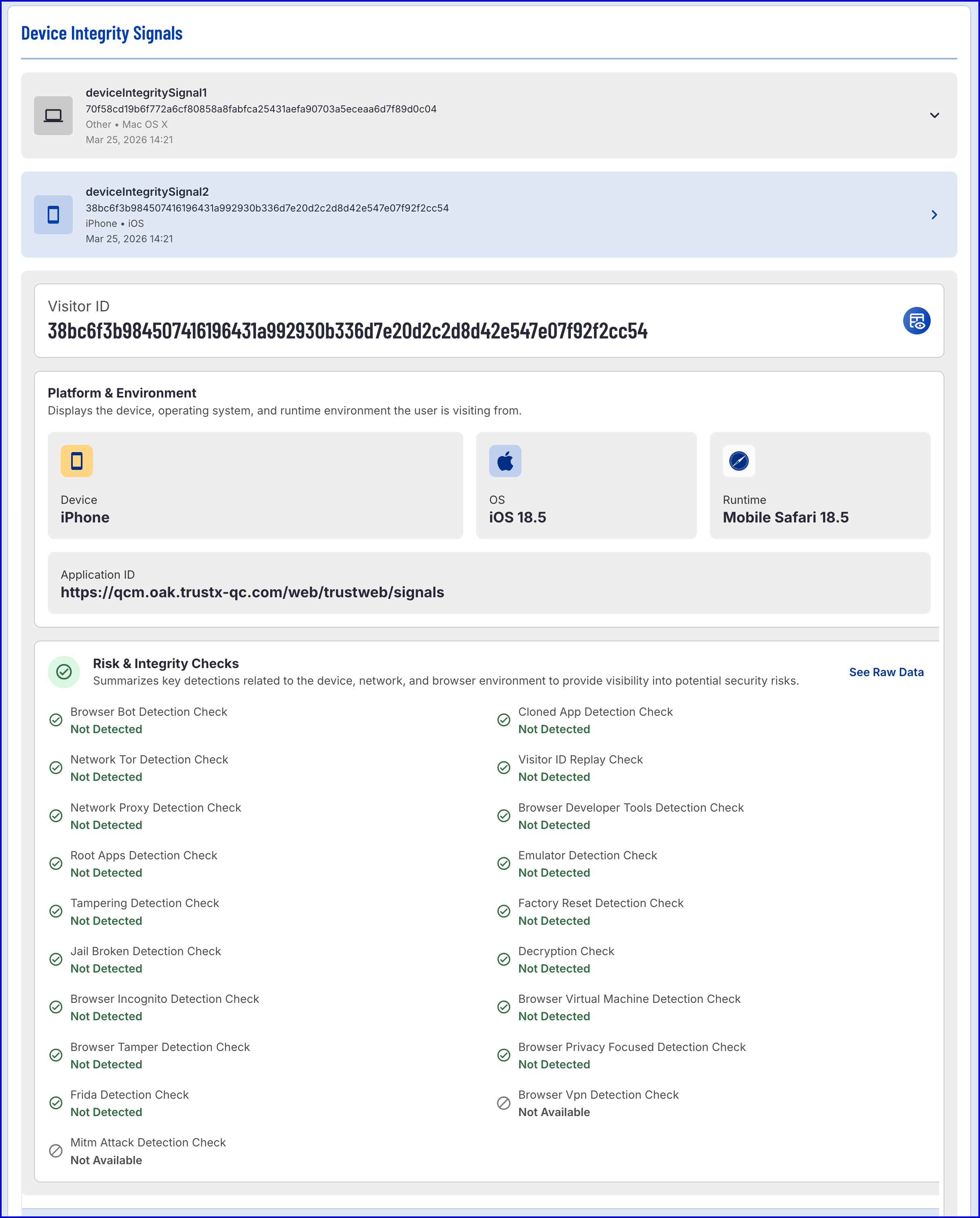
Example of a mobile response
From the example above, two Device Integrity Signals have been recorded. The first was recorded from a Mac device and the second was recorded from an iPhone. Data collected for each device includes the following:
| Item | Description |
|---|---|
| Visitor ID | The Visitor ID associated with the captured device. |
| Device | The type of device. For non-mobile devices, this field will be recorded as 'Other'. |
| OS | The operating system of the recorded device. |
| Runtime | The browser used to access the Trust Web application. |
| Application ID | The ID of the application. |
| Risk & Integrity Checks | The various risk and integrity checks performed on the device as part of the Process Instance and the resulting status. |
Add Visitor ID to Watchlist
The recorded Visitor ID can be added to an existing Watchlist of type 'Visitor ID' by using the supplied button in the Backoffice application.
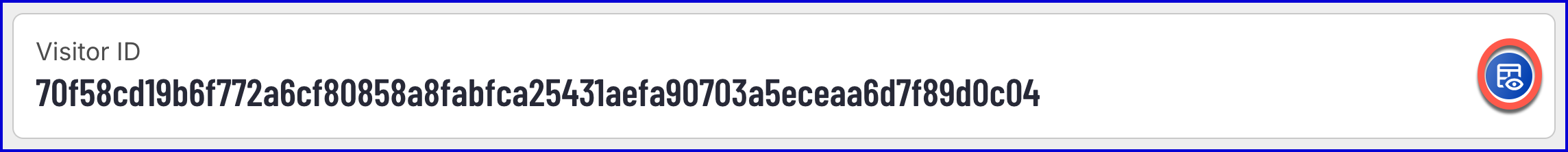
Clicking the button will open a pop-up modal where an existing Watchlist can be selected.
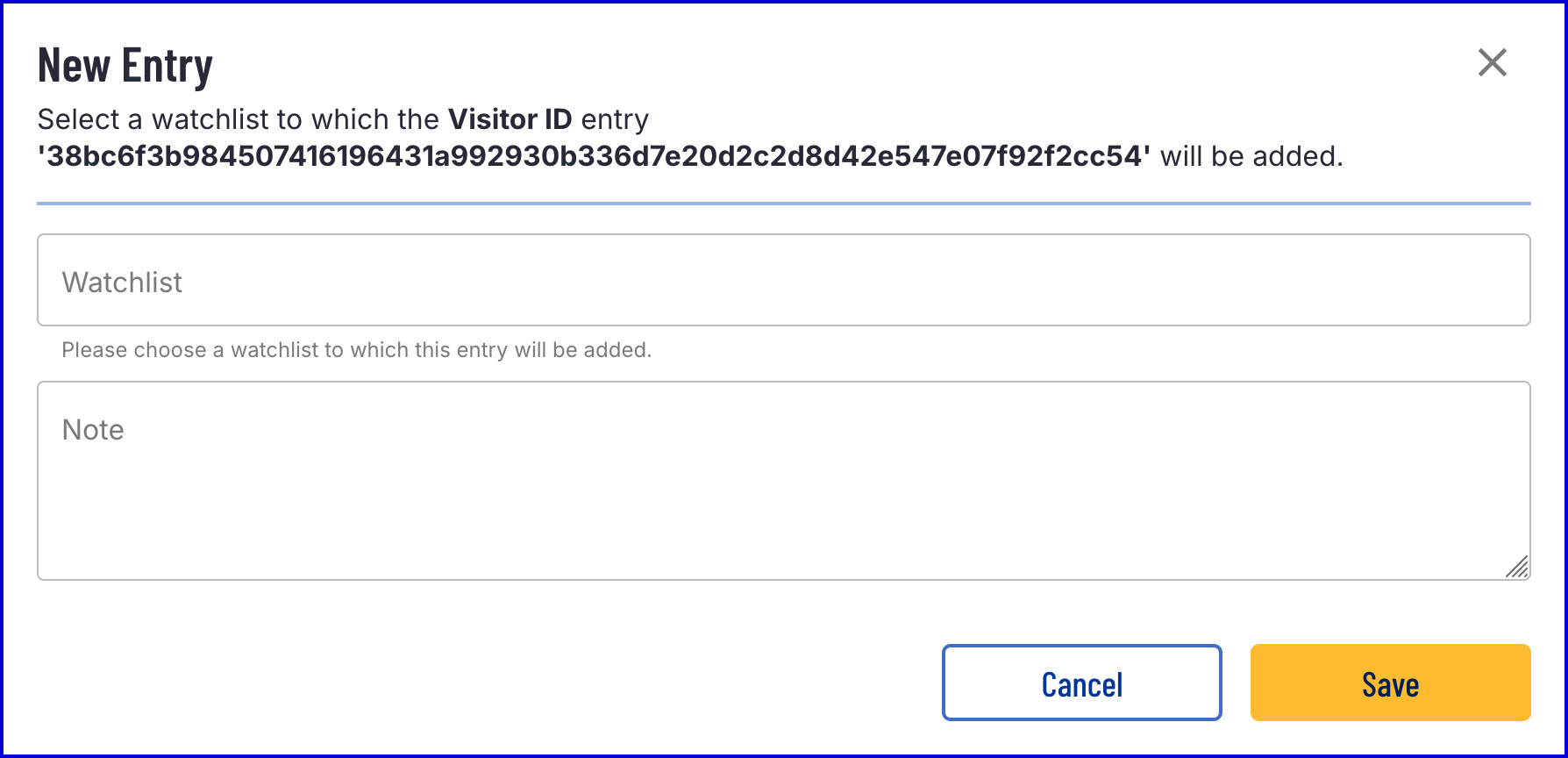
An existing Watchlist of type 'Visitor ID' is required before a new Watchlist member can be added. See Managing Watchlists for more information.
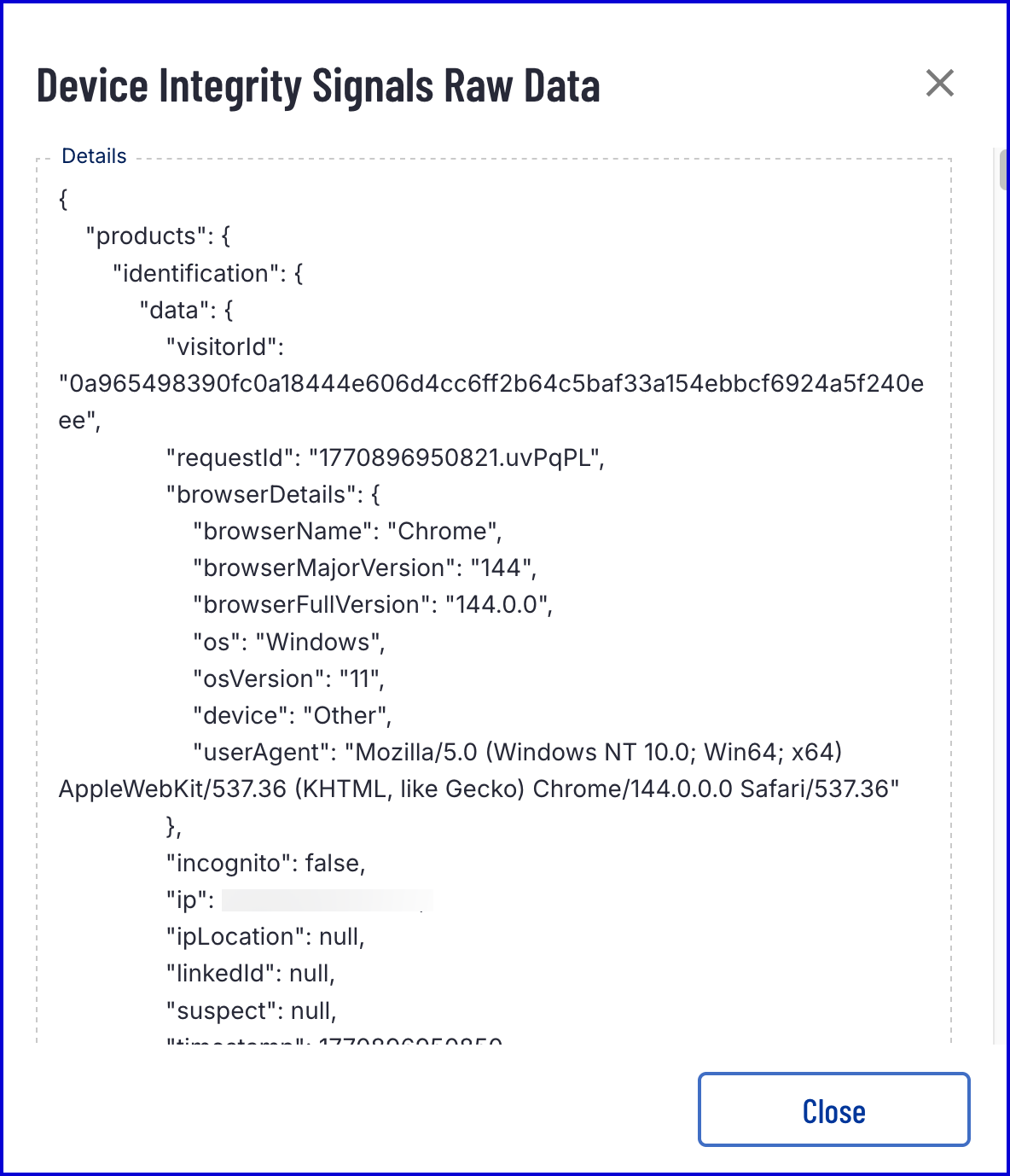
See Raw Data
By clicking the 'See Raw Data', a raw representation of the recorded device and integrity checks performed can be downloaded.
Native Mobile Integration
The Trust SDK provides a Device Integrity Signal module that can be integrated for native mobile integrations. For more information, see the relevant guides below: